 |
PRS821S - PROGRAMMING FOR SECURITY PERSONNEL - 2ND OPP - JAN 2024 |
 |
1 Page 1 |
▲back to top |

nAmlBIA UnlVERSITY
OF SCIEnCE Ano TECHnOLOGY
FACULTY OF COMPUTING AND INFORMATICS
DEPARTMENTOF SOFTWAREENGINEERING
QUALIFICATION: BACHELOROF COMPUTERSCIENCEHONOURS(SOFTWARE
DEVELOPMENT}
QUALIFICATIONCODE:08BCHS
LEVEL: 8
COURSE:PROGRAMMING FORSECURITY
PERSONNEL
DATE:JANUARY2024
COURSECODE:PRS821S
PAPER:THEORY
DURATION: 2 HOURS
MARKS: 100
SECONDOPPORTUNITY/SUPPLEMENTARYEXAMINATION QUESTIONPAPER
EXAMINER
DR AMBROSEAZETA
MODERATOR:
MR OMOBAYO AYOKUNLEESAN
INSTRUCTIONS
1. Answer ALL the questions.
2. Read all the questions carefully before answering.
3. Number the answers clearly.
THIS QUESTION PAPERCONSISTSOF 4 PAGES
(Including this front page}
1
 |
2 Page 2 |
▲back to top |
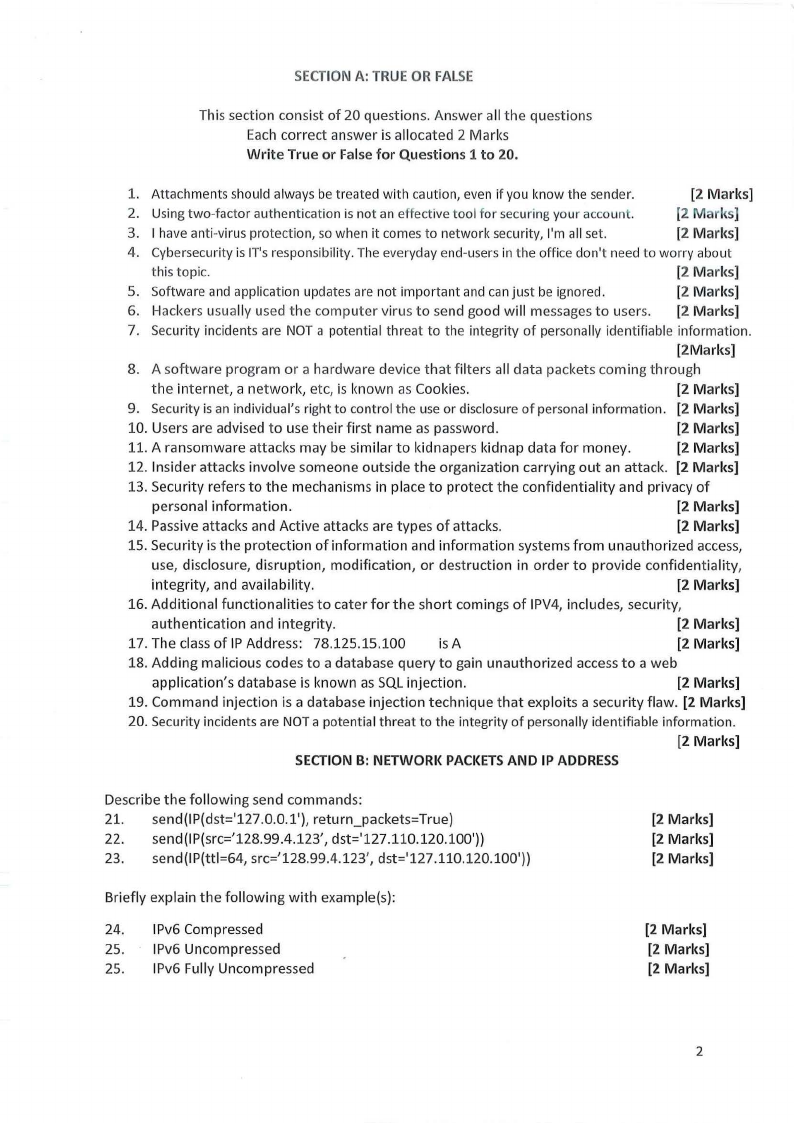
SECTIONA: TRUEOR FALSE
This section consist of 20 questions. Answer all the questions
Each correct answer is allocated 2 Marks
Write True or False for Questions 1 to 20.
1. Attachments should always be treated with caution, even if you know the sender.
[2 Marks]
2. Usingtwo-factor authentication is not an effective tool for securingyour account.
[2 Marks]
3. I have anti-virus protection, so when it comes to network security, I'm all set.
[2 Marks]
4. Cybersecurityis IT'sresponsibility. The everyday end-usersin the office don't need to worry about
this topic.
(2 Marks]
5. Software and application updates are not important and canjust be ignored.
[2 Marks]
6. Hackers usually used the computer virus to send good will messages to users. [2 Marks]
7. Security incidents are NOT a potential threat to the integrity of personally identifiable information.
[2Marks]
8. A software program or a hardware device that filters all data packets coming through
the internet, a network, etc, is known as Cookies.
[2 Marks]
9. Security is an individual's right to control the use or disclosureof personal information. [2 Marks]
10. Users are advised to use their first name as password.
[2 Marks]
11. A ransom ware attacks may be similar to kidnapers kidnap data for money.
[2 Marks]
12. Insider attacks involve someone outside the organization carrying out an attack. (2 Marks]
13. Security refers to the mechanisms in place to protect the confidentiality and privacy of
personal information.
[2 Marks]
14. Passive attacks and Active attacks are types of attacks.
(2 Marks]
15. Security is the protection of information and information systems from unauthorized access,
use, disclosure, disruption, modification, or destruction in order to provide confidentiality,
integrity, and availability.
(2 Marks]
16. Additional functionalities to cater for the short comings of IPV4, includes, security,
authentication and integrity.
(2 Marks]
17. The class of IP Address: 78.125.15.100
is A
[2 Marks]
18. Adding malicious codes to a database query to gain unauthorized access to a web
application's database is known as SQL injection.
(2 Marks]
19. Command injection is a database injection technique that exploits a security flaw. (2 Marks]
20. Security incidents are NOTa potential threat to the integrity of personally identifiable information.
[2 Marks]
SECTIONB: NETWORKPACKETSAND IP ADDRESS
Describe the following send commands:
21. send(IP(dst='127.0.0.1'), return_packets=True)
22. send(IP(src='128.99.4.123', dst='127.110.120.100'))
23. send(IP(ttl=64, src='128.99.4.123', dst='127.110.120.100'))
(2 Marks]
(2 Marks]
[2 Marks]
Briefly explain the following with example(s):
24. IPv6 Compressed
25. IPv6 Uncompressed
25. IPv6 Fully Uncompressed
(2 Marks]
(2 Marks]
(2 Marks]
2
 |
3 Page 3 |
▲back to top |
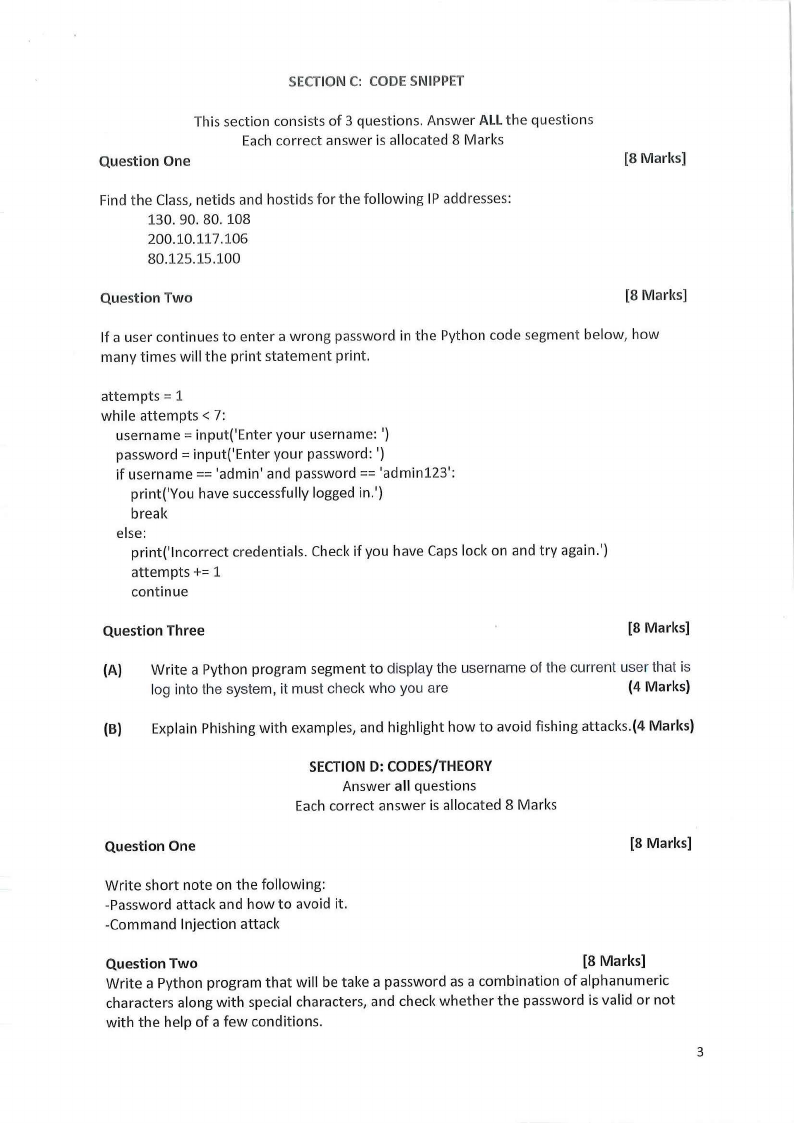
SECTIONC: CODESNIPPET
This section consists of 3 questions. Answer ALLthe questions
Each correct answer is allocated 8 Marks
Question One
(8 Marks]
Find the Class, netids and hostids for the following IP addresses:
130.90.80. 108
200.10.117.106
80.125.15.100
Question Two
[8 Marks]
If a user continues to enter a wrong password in the Python code segment below, how
many times will the print statement print.
attempts= 1
while attempts< 7:
username = input('Enter your username: ')
password = input('Enter your password: ')
if username == 'admin' and password== 'admin123':
print('You have successfully logged in.')
break
else:
print('lncorrect credentials. Check if you have Caps lock on and try again.')
attempts+= 1
continue
Question Three
[8 Marks]
(A) Write a Python program segment to display the username of the current user that is
log into the system, it must check who you are
(4 Marks)
(B) Explain Phishing with examples, and highlight how to avoid fishing attacks.(4 Marks)
SECTIOND: CODES/THEORY
Answer all questions
Each correct answer is allocated 8 Marks
Question One
[8 Marks]
Write short note on the following:
-Password attack and how to avoid it.
-Command Injection attack
Question Two
(8 Marks]
Write a Python program that will be take a password as a combination of alphanumeric
characters along with special characters, and check whether the password is valid or not
with the help of a few conditions.
3
 |
4 Page 4 |
▲back to top |

The primary conditions for password validation are as follows:
a. Minimum 8 characters.
b. The alphabet must be between [a-z]
c. At least one alphabet should be of Upper Case [A-Z]
d. At least 1 number or digit between [0-9].
e. At least 1 character from [_or @ or$ ].
Sample outputl
Input: R@m@_f0rtu9e$
Output : Valid Password
Sample output2
Input : Rama_fortune$
Output : Invalid Password
Explanation: Number is missing
Sample output3
Input: Rama#fortu9e
Output : Invalid Password
Explanation: Must consist from_ or@ or$
Question Three
[8 Marks]
Briefly discuss the following types of network topology - Ring, Mesh and Hybrid.
--THE
END
4





