 |
CMN620S - COMMUNICATION NETWORKS- 1ST OPP - NOV 2025 |
 |
1 Page 1 |
▲back to top |
nAm IBl A un IV ERSITY
OF SC IEnCE Ano TECHnOLOGY
FACULTY OF COMPUTING AND INFORMATICS
DEPARTMENT OF COMPUTER SCIENCE
QUALIFICATION: BACHELOR OF COMPUTER SCIENCE, BACHELOR OF CYBER SECURITY
QUALIFICATION CODE: 07BACS, 07BCCS
Level: 6
Course Name: Communication Networks
Course code: CMN620S
Date: November 2025
Paper: Theory
Duration: 3 hours
Marks: 70
Examiners
Moderator
First Opportunity Examination Question Paper
Ms. Albertina Shilongo
Mr. Edward Nepolo
THIS QUESTION PAPER CONSISTS OF 6 PAGES (Including this front page)
INSTRUCTIONS
1) Answer ALL the questions on the answer scripts provided.
2) Write clearly and neatly.
3) Be guided by the number of marks allocated when answering the questions.
4) Show all your calculations.
5) Number your questions clearly.
Permissible Material
1. Calculators.
1
 |
2 Page 2 |
▲back to top |
Question 1: True and False and Multiple Choice
Write the question number and answer only.
[10]
True/ False
a) The Stub Area in OSPF does not allow Type 5 (External) LSAs and receives a default route from the ABR
instead.
b) Autonomous System Boundary is the router in OSPF that connects of a non-OSPF network.
c) The ABR sends summarized routes from one area to another using Type 2 LSAs.
d) RIP uses TCP to ensure reliable delivery of its routing updates.
e) VLSM allows Network Administrators to use only the subnet masks for different subnets within the same
f) The address 10.255.255.255/8 is a usable host address on a network
g) A primary function ofVLANs is to create multiple single broadcast domains.
h) An Access port is mainly used to connect a switch to another switch and carry multiple VLAN traffic.
i) ISPs primarily generates their IP address blocks directly from a local company.
j) In BGP, the path with the highest LOCAL_PREF value is preferred.
Multiple choice Questions
a) A router running RIP has not received updates from its neighbors in 190 seconds. What subsequent
actions are taken by the router?
a) Send a request to re-establish neighborship
b) Delete all routes from the routing table
c) Consider the neighbour unreachable and update the routing table accordingly.
d) Keeps waiting for updates for an hour
b) The primary function of IGPs, such as RIP or OSPF is:
a) To connect various AS together.
b) To route traffic across the Internet.
c) To enable routers to exchange routing information within a single Autonomous System.
d) To provide filtering of external traffic.
c) Which router maintains generates Type 3 LSA and separate LSDBs for each area it connects in a multi-
area OSPF network?
a) Internal Router
b) Backbone Router
c) Autonomous System Border Router {ASBR)
d) Area Border Router (ABR)
d) A network architect is designing new campus network with the main requirement of providing fast
routing between several user VLANs and a centralized server block, within the same building. Which
device should be the primary choice for this role.
a) NGFW provides security filtering between subnets.
b) A high-end Router has advanced BGP and WAN routing capabilities.
2
 |
3 Page 3 |
▲back to top |
c) A Layer 3 Switch as it makes routing decisions using its hardware multi-gigabit speeds equipped
in its hardware.
d) A Layer 3 Switch as it is equipped with multiple ports unlike a high-end router.
e) When configuring RIP, what does the command network 192.168.10.0 inform the router?
a) Advertise the specific 192.168.10.0/24 network and participate in RIP on any interface with
an IP address belonging to the classful 192.168.10.0 network.
b) Assign the IP address 192.168.10.0 to the closest available interface.
c) Only advertise the 192.168.10.0 network if it is directly connected to the router.
d) Create a new network with the address 192.168.10.0 and wait for other routers to join.
f) What is the purpose of configuring a console password on a router?
a) To encrypt all traffic passing through the router's interfaces.
b) To enforce authentication for remote network access via Telnet or SSH.
c) To enforce authentication when accessing the physical access to the router's command-
line interface (CLI) via the console port.
d) To secure privileged EXEC mode and prevent unauthorized access to the enable command.
g) Consider a class Bnetwork address 172.16.0.0 /19. By applying CIDR, how many subnets and usable hosts
will be provided?
a) 7 networks and 2046 hosts
b) 7 networks and 8190 hosts
c) 8 networks and 2046 hosts
d) 8 networks and 8190 hosts
h) Which OSI layer does IP rely on to determine whether packets have been lost and to request for
retransmission?
a) Application
b) Presentation
c) Transport
d) Data link
i) The enable secret password is configured to protect access to which router mode?
a) User EXEC Mode
b) Global Configuration
c) Privilege Mode
d) Interface Configuration Mode
j) What are/is the characteristics of the IP address 255.255.255.255
a) A reserved IP address
b) Addressing all hosts on the local network.
c) Unavailable for configuration on any interface.
d) All the above
3
 |
4 Page 4 |
▲back to top |
Queston 2: Explain the following concepts
[10]
a} Distance-Vector Routing Algorithm
b) Intra-AS Routing
c) Interior Gateway Protocol (IGP)
d) Port-based VLANs
e) Variable Length Subnet Masking
Question 3: Long questions
[14]
1. A company has a single 48-port switch configured with the following three VLANs:
• VLAN 10 (Sales): Ports 1-8, subnet: 192.168.10.0/24
• VLAN 20 (HR): Ports 9-16, subnet: 192.168.20.0/24
• VLAN 30 (Finance}: Ports 17-24, subnet: 192.168.30.0/24
PC A (IP: 192.168.10.5) in VLAN 10 needs to communicate with a network printer (IP: 192.168.20.10) which
is in VLAN 20. The network uses a Router-on-a-Stick configuration for inter-VLAN routing, with the router
interface configured as follows:
• Sub-interface Fa0/0.10: IP 192.168.10.1 for VLAN 10
• Sub-interface Fa0/0.20: IP 192.168.20.1 for VLAN 20
a) Explain step-by-step how ARP resolves the MAC addresses needed when the PC-A sends its first
communication to access the printer.
(6)
b) If the port connecting the switch and the router is configured as an access port, the communication
between the PC-A and the printer will fail even after the steps you outlined in A are correctly actioned.
Why is that the case?
(4)
c) If the router is rep laced with a Layer 3 switch, what are the fundamental configurations that need to be
made to ensure that traffic between VLAN 10 and VLAN 20 is handled successfully?
(4)
4
 |
5 Page 5 |
▲back to top |
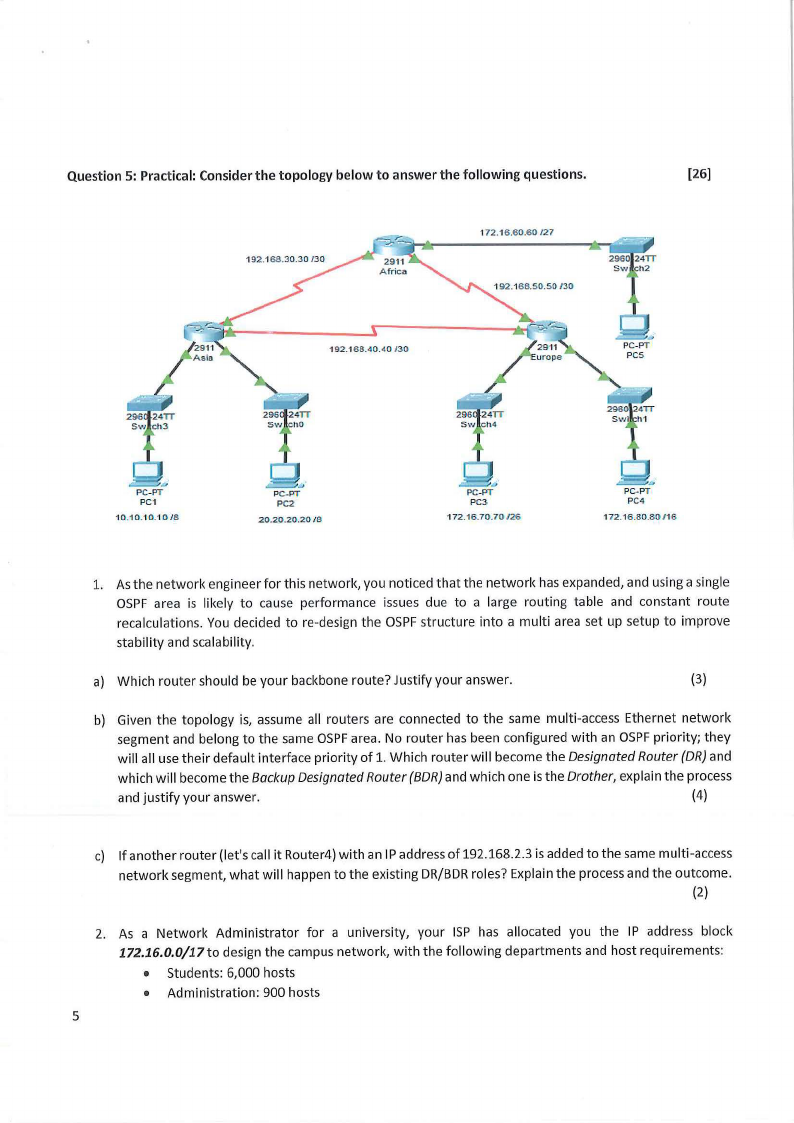
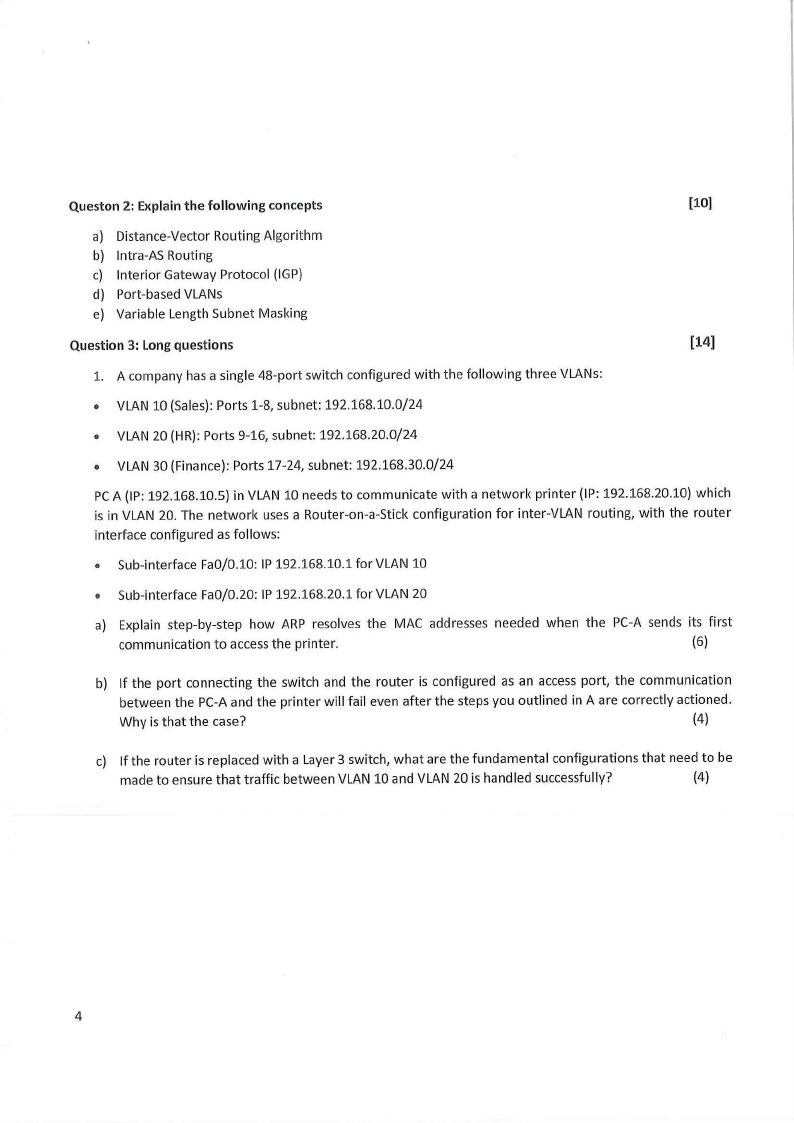
Question 5: Practical: Consider the topology below to answer the following questions.
[26]
172.16 .60.60/27
192.1 68.40.4 0 /30
2911
-
u rope
/
= ~ ..,
PC-PT
PCS
1 0 .1 0.1 0. 10/8
~.,
PC-PT
PC2
20.20.20.20 /8
172.16.70.70/26
,ll,;....- h J
PC-PT
PC4
172.16 .80.80 / 16
1. As the network engineer for this network, you noticed that the network has expanded, and using a single
OSPF area is likely to cause performance issues due to a large routing table and constant route
recalculations. You decided to re-design the OSPF structure into a multi area set up setup to improve
stability and scalability.
a) Which router should be your backbone route? Justify your answer.
(3)
b) Given the topology is, assume all routers are connected to the same multi-access Ethernet network
segment and belong to the same OSPF area. No router has been configured with an OSPF priority; they
will all use their default interface priority of 1. Which router will become the Designated Router {DR) and
which will become the Backup Designated Router (BDR) and which one is the Drother, explain the process
and justify your answer.
(4)
c) If another router (let's call it Router4) with an IP address of 192.168.2.3 is added to the same multi-access
network segment, what will happen to the existing DR/BDR roles? Explain the process and the outcome.
(2)
2. As a Network Administrator for a university, your ISP has allocated you the IP address block
172.16.0.0/17 to design the campus network, with the following departments and host requirements:
• Students: 6,000 hosts
• Administration: 900 hosts
5
 |
6 Page 6 |
▲back to top |
• Finance: 400 hosts
• HR: 25 hosts
a) Using a Fixed-Length Subnet Mask approach, design the network that satisfy these requirements and
determining the following: The subnet address and broadcast address for each subnet. Show all your
calculations.
(8)
b) After reviewing your network design for the 172.16.0.0/17 block, your manager points out the significant
inefficient al location of IP addresses, most especially for the smaller and suggested that you redesign the
network using the IP addressing scheme that is efficient. Which IP address scheme is the manager
suggesting?
(1)
c) Using the efficient IP address scheme suggested by your manager in B, determine the subnet address
and subnet mask for each subnet. Show all your calculations.
(8)
Exam Ends
6





