 |
DTN611S - DATA NETWORK - 2ND OPP - JULY 2025 |
 |
1 Page 1 |
▲back to top |
n Am I BI A u n IVER s I TY
OF SCIEnCE Ano
FACULTYOF COMPUTING AND INFORMATICS
DEPARTMENTOF COMPUTERSCIENCE
QUALIFICATION:BACHELOROF COMPUTERSCIENCE,BACHELOROF INFORMATICS
QUALIFICATIONCODE:07BACS,07BAIF
LEVEL:7
>-·
·-
COURSENAME: DATA NETWORK
COURSECODE: DTN611S
DATE:JULY2025
PAPER:THEORY
DURATION:3 HOURS
MARKS: 80
SECOND/SUPPLEMENTARYOPPORTUNITYEXAMINATION QUESTION PAPER
EXAMINER
MS. ALBERTINASHILONGO
·-
MODERATOR
MS. LOINI IIYAMBO
THISQUESTIONPAPERCONSISTSOF 6 PAGES(including this front page)
INSTRUCTIONS
1) Answer ALL the questions on the answer scripts provided.
2) Write clearly and neatly.
3) Be guided by the number of marks allocated when answering the questions.
4) Show all your calculations.
5) Number your questions clearly.
Permissible Material
1. Calculators.
pg. 1
 |
2 Page 2 |
▲back to top |
Question 1: Multiple Choice, True or False and short questions
(1 mark each)
1. What is the binary equivalence of 222.1.3.27?
a) 11011111.00000001.00000011.00011100
b) 11000000.10100100.00000010.00011000
c) 01100000.11101000.00000010.00011000
d) 11000000. 10101000.00000011.00011000
[20 Marks]
2. Which network techniques enable devices on a private network to accessthe internet by using
a single public IP address.
a) Adress Translation Protocol (ATP)
b) Domain Name System (DNS)
c) Port Address Translation (PAT)
d) Network Address Translation (NAT)
3. Which of the following layer's primary functions is to transmit/move
another adjacent node over a single communication link?
a) Network Layer
b) Session Layer
c) Physical Layer
d) Data Link Layer
data from one node to
4. The Three-way handshake messages establish and terminate a connection in which sequence.
a) SYN, ACK, SYN-ACK, ACK-FIN
b) SYN,SYN-ACK,ACK, FIN-ACK
c) SYN,SYN-ACK,ACK, FIN-FIN
d) SYN,SYN-ACK,FIN, ACK-FIN
5. What is the process of wrapping packets with the necessary header/protocol
before the packet is transmitted to the next layer of OSI.
a. Encapsulation
b. Encoding
c. Decapsulation
d. Decoding
information
6. Which layer of the OSI model performs flow control
a) Network and Transport Layers
b) Application and Data Link Layers
c) Session and Application
d) Transport and Datalink Layers
pg. 2
 |
3 Page 3 |
▲back to top |
7. The default subnet mask for ClassA IP address is:
a) /18
b) /9
c) /16
d) /8
8. What is the main purpose of a wireless access point (AP)?
a) To extend wired network signals
b) To provide internet to end devices on the networks
c) Connect Wi-Fi- devices to a wired network using wireless signals.
d) To store network data
9. LTEis primarily designed for which type of network communication?
a) Long -range metropolitan networks
b) Long-range cellular networks
c) Local area networks only
d) Satellite communication
10. What is the advantage of satellite communication?
a) Low data latency
b) Low power consumption
c) Wide area coverage
d) Increased data security
11. What is the requirement for infrared communication to work?
a) A direct line of sight
b) A radio tower
c) A cloud server
d) Satellite link
12. What is th~ binary representation of this Hexadecimal value FEB24?
a) 11111011 0010 0100
b) 11111110 0100 1010
c) 11111011 0101 0100
d) 11111110 0010 0100
13. Identify the network application protocol responsible for performing the following actions. No
abbreviations are allowed.
(a) Fetching a web document from a web server:
(b) Uploading a document onto a File server:
pg. 3
 |
4 Page 4 |
▲back to top |
(c} Configuring your office router from a remote location:
(d} Resolving the IP address of a specified domain
(e) Accessing electronic mail from the client's mail server on any of the client's devices.
(f) Downloading the recipient e-mail to the client's device and erase it from the mail server.
14. The physical medium can take many shapes and forms and does not have to be of the same
type for each transmitter-receiver pair along the path.
a) True
b) False
15. Every application using UDP should always establish a three-way handshake before it.
Can transmit data.
(a) True
(b) False
Question 2
[10 marks]
James was recently hired as an IT Technician at Young Tech CC.The company purchased 200 new
laptops for its employees. The IT Manager tasked James with configuring the devices so that they
could connect to the company's internal network and accessthe Internet.
a} List and explain the settings thatJames will MOST LIKELYneed to configure on each laptop to
achieve this goal.
(4)
b} To configure all 200 laptops efficiently, James decides to configure the DHCPserver. what are
the 2 primary benefits of using DHCPin this situation?
(2)
c} Assuming that there is a single DHCPserver on the network, what would happen if this DHCP
server goes offline?
(2)
d} After setting up the network, a user came to James complaining that they can access the
company's website and download files from the local servers, but they cannot access the
Internet. What are the two possible causes of this issue?
(2)
QUESTION 3
[22 Marks]
a} Explain the importance of the 3-way handshake in TCP reliable data transmission.
(2)
b} List and explain the three steps of the TCP3-way handshake.
(6)
c} In the 3-way handshake process, the client sends the initial packet with a sequence number of
1000. The server responds with a packet recognizing the initial packet it received and begins its
own sequence starting at 5000.
d) what would be the next sequence number in the ACK packet?
(2)
e) What will be the sequence number of the packet that the client sends to the server to establish
the connection?
(2)
pg.4
 |
5 Page 5 |
▲back to top |
f) What will be the sequence number of the first request packet sent by the client to the server
(2)?
g) If the final packet sent by the client to the server in establishing a 3-way handshake gets lost in
the process, how will TCP handle this situation?
(2)
h) Explain the role of the FIN and ACKflags in the TCP.
(4)
Question 4
[20 marks]
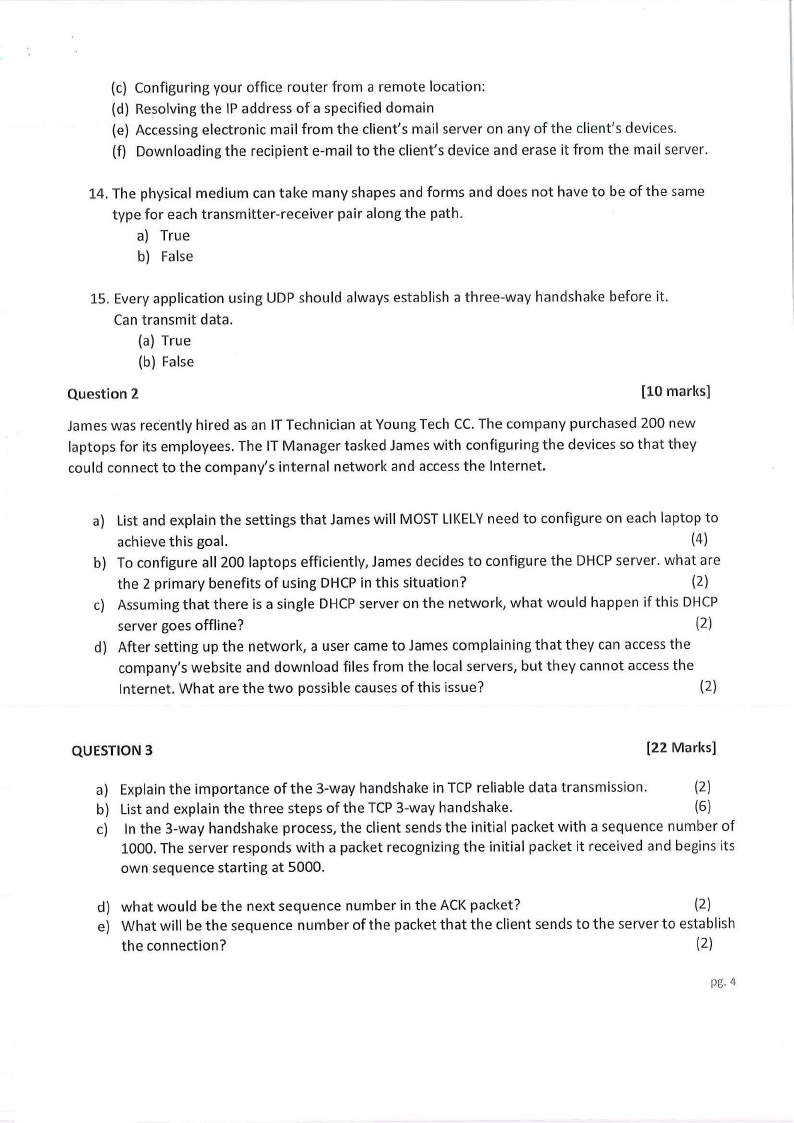
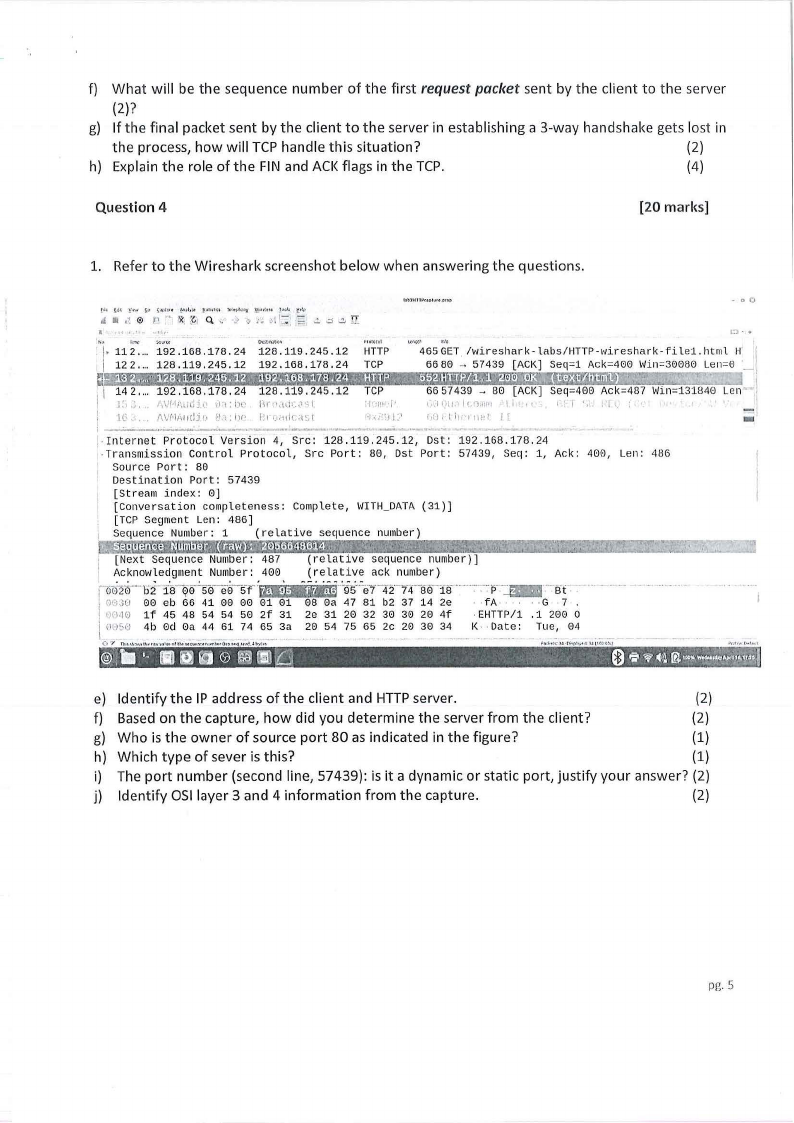
1. Refer to the Wireshark screenshot below when answering the questions.
- 00
[•1 .lH ~•"'"
~..,h,.u ~,1,zt ~,1.,t,,t1 Tt'.-i.t,:ry ~Ol.{OI ,!OW ~•!.l
J .~ @ r, " ~- '.G1 , ., '> , • ~I 1:: ;;:; .::. .::; w lI
JI
I
' ,,
l:J •
r,otcrol
'. ,. 112 .... 192.168.178.24 128.119.245.12 HTTP 465GET. /wireshark-labs/HTTP-wireshark-filel.html
K
122 .... 128.119,245.12 192.168,178.24 TCP
66 80 -· 57439 (ACK) Seq=1 Ack=400 Win=30080 Len=0 ·_
~e~:-.~~~.: !'.l!!f\\'$ftt&MHNt{~11tlif5WiiSiJ:S%ffii:@ffHt
11 7~ :--·
1~~: ~;~- 1~~;:f45 .12 ~~:. ,.
I IG
/\\\\/(·JA11(lj!1 f·),t,ll( 1 1!1,.1,-HIC,\\~,l
•J.,, 'JI~'
-
•
_____
,..__
...... _
-·
•
l&,I
•
....
--
... __
·~--·-
-
1
6657439 - 80 [ACK) Seq=400 Ack=487 Win=131840 Len ,
, "'.ii, , , 0.111•1 , 1 1 •
ldJ I I i1 1 rn:I fr
r 1 , • ,, •
-
. Internet Protocol Ve-rsion 4, Src: 128 .119, 245 .12, Dst: 192 .168 .178. 24
-Transmission Control Protocol, Src Port: 80, Dst Port: 57439, Seq: 1, Ack: 400, Len: 486
Source Port: 80
Destination Port: 57439
(Stream index: 0)
(Conversation completeness: Complete, WITH_DATA(31))
... . (TCP Segment Len: 486)
Sequence Number: 1 (relative
1
;
sequence number)
[Next Sequence Number: 487 (relative sequence number))
A. c'know.l.ed.gment.
Nwnber: 400
'
,
,0020 b2 18 Q0 50 e0 5f
. fll'1JO 00 eb 66 41 00 00 01 01
I I fl,10 1f 45 48 54 54 50 2f 31
I i·H·J[,o 4b 0d 0a 44 61 74 65 3a
L. -- -•--•·.-- .. --·---- --··--·- 0 'l T)l-,...,,..,,1t,,,,~~•l<>&ottl).>u~iw:~rurt••fi<P'-"'l
.,.., Jt,,,:-.
(relative ack number)
--· ·---·95-e7 4274-80 18·----_-·.--·p._ ·-Bt
08 0a 47 81 b2 37 14 2e
2e 31 20 32 30 30 20 4f
20 54 75 65 2c 20 30 34
• •fA • • · -G · 7
·EHTTP/1 ,1 200 0
K· •Date: Tue, 04
e) Identify the IP address of the client and HTTPserver.
(2)
f) Based on the capture, how did you determine the server from the client?
(2)
g) Who is the owner of source port 80 as indicated in the figure?
(1)
h) Which type of sever is this?
(1)
i) The port number (second line, 57439): is it a dynamic or static port, justify your answer? (2)
j) Identify OSI layer 3 and 4 information from the capture.
(2)
pg.5
 |
6 Page 6 |
▲back to top |
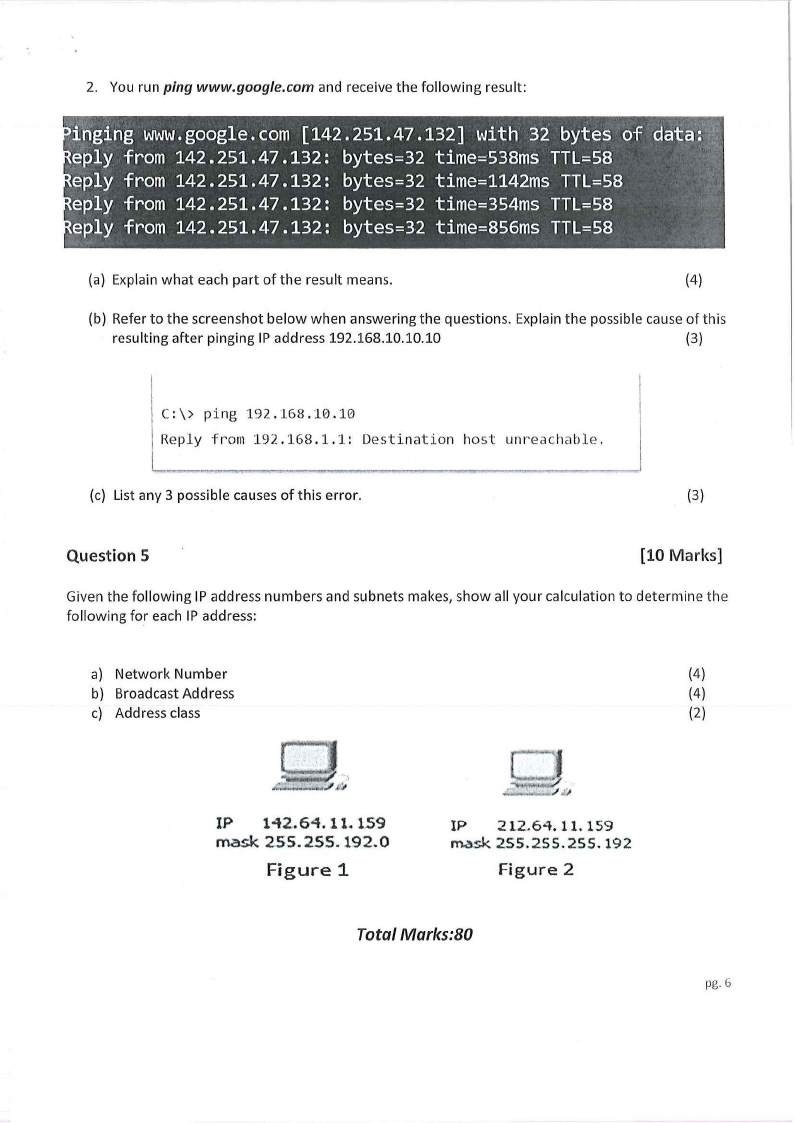
2. You run ping www.google.com and receive the following result:
dai~Yli '·)r,ging WWWg. oogle. com [142. 251. 47.132] with 32 bytes of
~ply from 142. 251.47 .132: bytes=32 time=538ms TTL=58
· :\\
·eply from 142.251.47.132: bytes=32 time=1142ms TTL=58
·
eply from 142.251.47.132: bytes=32 time=354ms TTL=58
eply from 142.251.47.132: bytes=32 time=856ms TTL=58
(a) Explain what each part of the result means.
(4)
(b) Refer to the screens hot below when answering the questions. Explain the possible cause of this
resulting after pinging IP address 192.168.10.10.10
(3)
C:\\> ping 192.168.10.10
Reply from 192.168.1.1: Destination host unreachable.
L-~--------~-____,
(c) List any 3 possible causes of this error.
(3)
Question 5
[10 Marks]
Given the following IP address numbers and subnets makes, show all your calculation to determine the
following for each IP address:
a) Network Number
(4)
b) Broadcast Address
(4)
c) Address class
(2)
IP 142.64. 11. 159
mask 255. 255. 192.0
Figure 1
IP 212.64. 11. 159
rn.c,sk2.SS.255.25S.192
Figure 2
Total Marks:80
pg. 6





