 |
SAD622S - SYSTEMS ADMINISTRATION - 2ND OPP - DEC 2025 |
 |
1 Page 1 |
▲back to top |
nAm l BI A Un l VERSITY
OF SC IEnC E Ano TECHnOLOGY
Faculty of Computing & Informatics
DEPARTMENT OF COMPUTER SCIENCES
QUALIFICATION : BACHELOR OF COMPUTER SCIENCE
QUALIFICATION CODE: 07BCMS & O7BCCY
LEVEL: 7
COURSE: SYSTEMS ADMINISTRATION
COURSE CODE: SAD622S
DATE: DECEMBER 2025
DURATION: 2 HOURS
PAPER: THEORY
MARKS: 80
SECOND OPPORTUNITY/ SUPPLEM ENTARY EXAMINATION QUESTION PAPER
EXAMINER(S) MR. PETER GALLERT
MODERATOR: MR. ISAAC NHAMU
THIS QUESTION PAPER CONSISTS OF 9 PAGES
(Excluding this front page)
Instructions for the candidate
1. Answer ALL questions.
2. When writing take the following into account: The style should inform than impress, it
should be formal, in third person, paragraphs set out according to ideas or issues and the
paragraphs flowing in a logical order.
3. Information should be brief and accurate.
4. Please ensure that your writing is legible, neat and presentable.
 |
2 Page 2 |
▲back to top |
Faculty of Computing and Informatics, Department of Computer Science
SAD622S: 2nd Opportunity Examination
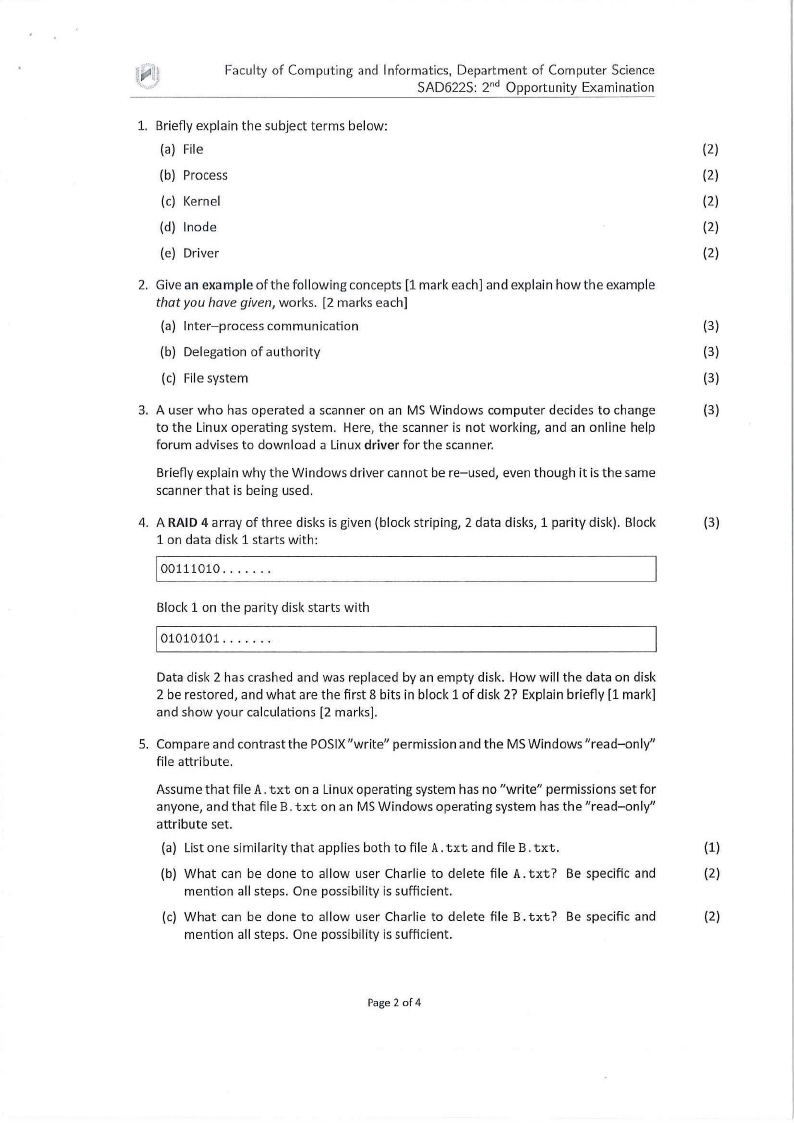
1. Briefly explain the subject terms below:
(a) Fi le
(2)
(b) Process
(2)
(c) Kernel
(2)
(d) lnode
(2)
(e) Driver
(2)
2. Give an example of the following concepts (1 mark each] and explain how the example
that you have given, works. (2 marks each]
(a) Inter-process communication
(3)
(b) Delegation of authority
(3)
(c) Filesystem
(3)
3. A user who has operated a scanner on an MS Windows computer decides to change
(3)
to the Linux operating system. Here, the scanner is not working, and an onl ine help
forum advises to download a Linux driver for the scanner.
Briefly explain why the Windows driver cannot be re-used, even though it is the same
scanner that is being used.
4. A RAID 4 array of three disks is given (block striping, 2 data disks, 1 parity disk). Block
(3)
1 on data disk 1 starts with :
100111010 ... . . . .
Block 1 on the parity disk starts with
101010101 . .. .. . .
Data disk 2 has crashed and was replaced by an empty disk. How w ill the data on disk
2 be restored, and what are the first 8 bits in block 1 of disk 2? Explain briefly (1 mark)
and show your calculations (2 marks].
5. Compare and contrastthe POSIX"write" permission and the MS Windows "read-only"
file attribute.
Assume that file A. txt on a Linux operating system has no "write" permissions set for
anyone, and that file B. txt on an MS Windows operating system has the "read-only"
attribute set.
(a) List one similarity that applies both to file A. txt and file B. txt.
(1)
(b) What can be done to allow user Charlie to delete fi le A. txt? Be specific and
(2)
mention all steps. One possibility is sufficient.
(c) What can be done to allow user Charlie to delete file B. txt? Be specific and
(2)
mention all steps. One possibility is sufficient.
Page 2 of 4
 |
3 Page 3 |
▲back to top |
Faculty of Computing and Informatics, Department of Computer Science
SAD622S: 2nd Opportunity Examination
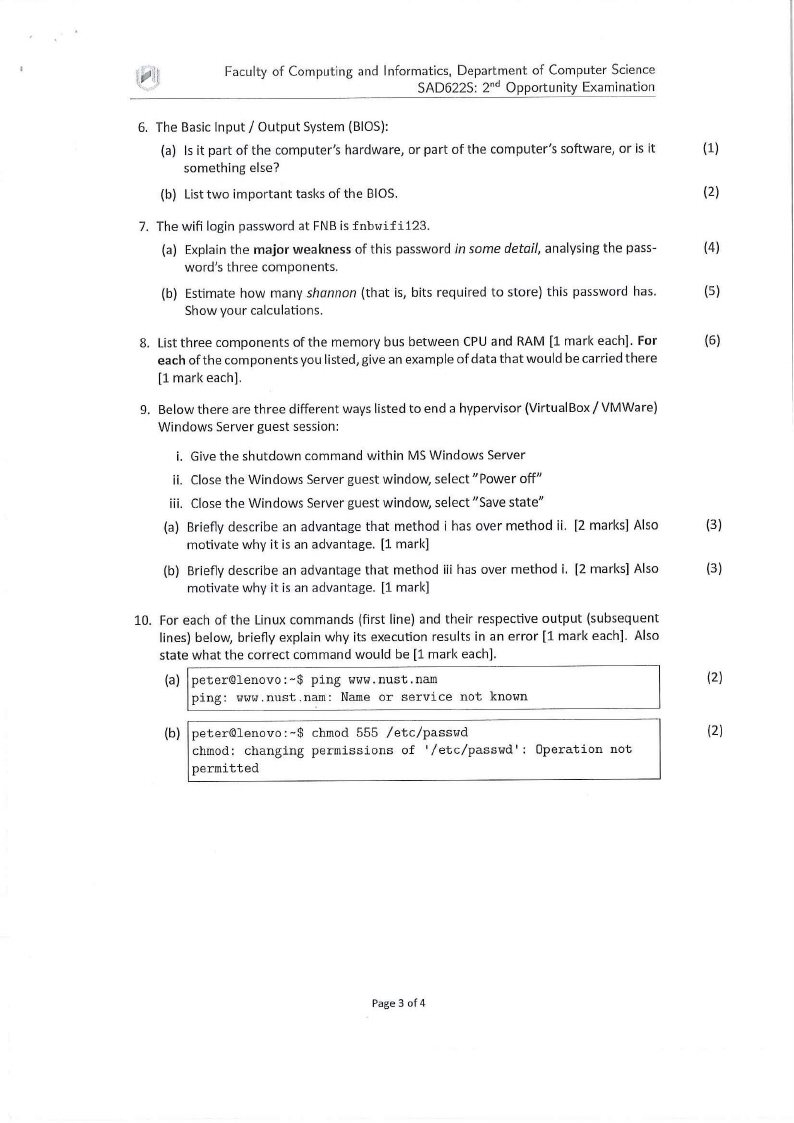
6. The Basic Input/ Output System (BIOS):
(a) Is it part of the computer's hardware, or part of the computer's software, or is it
(1)
something else?
(b) List two important tasks of the BIOS.
(2)
7. The wifi login password at FNB is fnbwifi123.
(a) Explain the major weakness of this password in some detail, analysing the pass-
(4)
word's three components.
(b) Estimate how many shannon (that is, bits required to store) this password has.
(5)
Show your calculations.
8. List three components of the memory bus between CPU and RAM [1 mark each]. For
(6)
each of the components you listed, give an example of data that would be carried there
[1 mark each].
9. Below there are three different ways listed to end a hypervisor (Virtual Box/ VMWare)
Windows Server guest session:
i. Give the shutdown command within MS Windows Server
ii. Close the Windows Server guest window, select "Power off"
iii. Close the Windows Server guest window, select "Save state"
(a) Briefly describe an advantage that method i has over method ii. [2 marks] Also
(3)
motivate why it is an advantage. [1 mark]
(b) Briefly describe an advantage that method iii has over method i. [2 marks] Also
(3)
motivate why it is an advantage. [1 mark]
10. For each of the Linux commands (first line) and their respective output (subsequent
lines) below, briefly explain why its execution results in an error [1 mark each]. Also
state what the correct command would be [1 mark each].
(a) peter©lenovo: -$ ping www. nust. nam
(2)
ping: www.nust.nam: Name or service not known
(b) peter©lenovo:-$ chmod 555 /etc/passwd
(2)
chmod: changing permissions of '/etc/passwd': Operation not
permitted
Page 3 of 4
 |
4 Page 4 |
▲back to top |
Faculty of Computing and Informatics, Department of Computer Science
SAD622S: 2nd Opportunity Examination
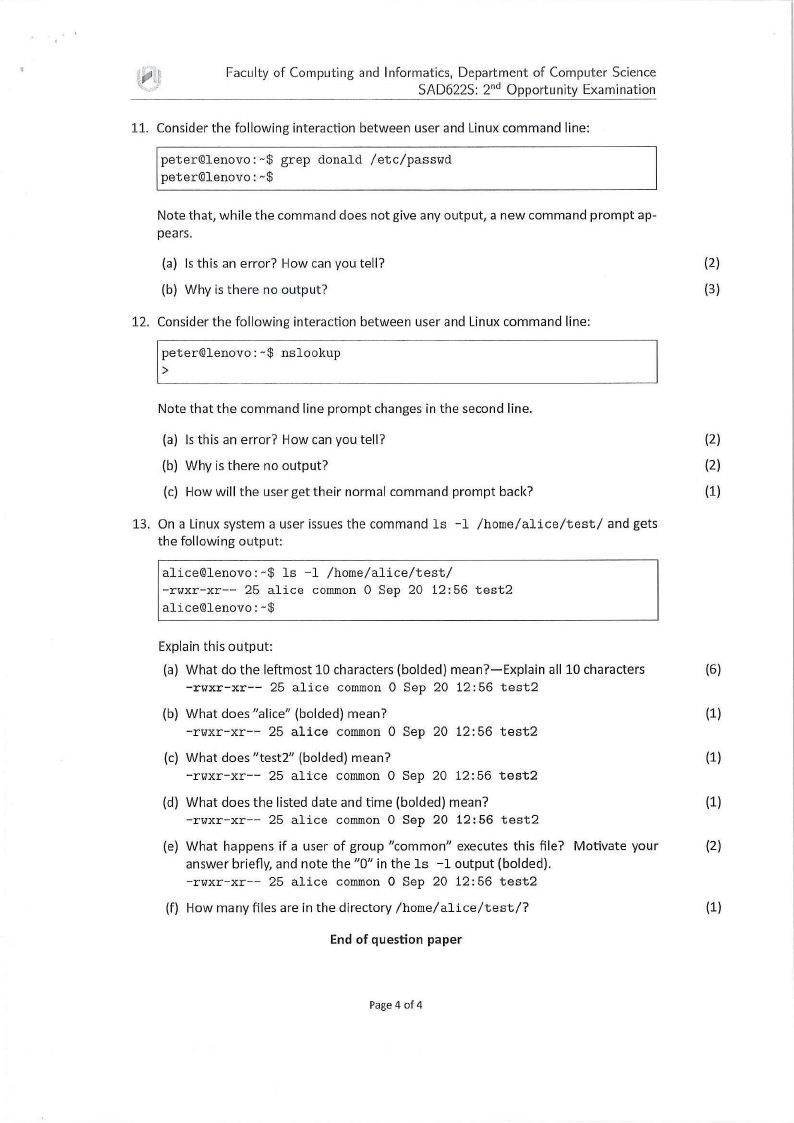
11. Consider the following interaction between user and Linux command line:
peter©lenovo:-$ grep donald /etc/passwd
peter©lenovo:-$
Note that, while the command does not give any output, a new command prompt ap-
pears.
(a) Is this an error? How can you tell?
(2)
(b) Why is there no output?
(3)
12. Consider the following interaction between user and Linux command line:
l;eter©lenovo,-$ nslookup
Note that the command line prompt changes in the second line.
(a) Is this an error? How can you tell?
(2)
(b) Why is there no output?
(2)
(c) How will the user get their normal command prompt back?
(1)
13. On a Linux system a user issues the command ls -1 /home/alice/test/ and gets
the following output:
alice©lenovo:-$ ls -1 /home/alice/test/
-rwxr-xr-- 25 alice common O Sep 20 12:56 test2
alice©lenovo: -$
Explain this output:
(a) What do the leftmost 10 characters (balded) mean?-Explain all 10 characters
(6)
-rwxr-xr-- 25 alice common O Sep 20 12:56 test2
(b) What does "alice" (balded) mean?
(1)
-rwxr-xr-- 25 alice common O Sep 20 12 :56 test2
(c) What does "test2" (bolded) mean?
(1)
-rwxr-xr-- 25 alice common O Sep 20 12:56 test2
(d) What does the listed date and time (balded) mean?
(1)
-rwxr-xr-- 25 alice common O Sep 20 12 :56 test2
(e) What happens if a user of group "common" executes this file? Motivate your
(2)
answer briefly, and note the "0" in the ls -1 output (bolded).
-rwxr-xr-- 25 alice common O Sep 20 12:56 test2
(f) How many files are in the directory /home/alice/test/?
(1)
End of question paper
Page 4 of 4





