 |
OPS611S - OPERATING SYSTEMS - 2ND OPP - JULY 2025 |
 |
1 Page 1 |
▲back to top |
n Am I BI A u n IVER s ITY
OF SCIEnCE Ano TECHnOLOGY
Faculty of Computing and Informatics
Department of Computer Science
QUALIFICATION: Bachelor of Computer Science in Cyber Security
Bachelor of Computer Science
Bachelor of Geoinformation Technology
Bachelor of Informatics
QUALIFICATIONCODE: 07BCCY,07BCMS, 07BGEI, LEVEL:6
07BAIT
COURSE:Operating Systems
COURSECODE: OPS611S
DATE:July 2025
SESSION: 2
DURATION: 2 hours 30 minutes
MARKS: 80
SECONDOPPORTUNITY/ SUPPLEMENTARYEXAMINATION QUESTION PAPER
EXAMINER(S}:
Mr. Nasimane Ekandjo
MODERATOR:
Ms. Loini liyambo
THIS QUESTION PAPERCONSISTSOF 6 PAGES
(Excluding this front page)
INSTRUCTIONS
1. Answer ALL the questions.
2. Write clearly and neatly.
3. Number the answers clearly.
4. When answering questions you should be guided by the allocation of
marks. Do not give too few or too many facts in your answers.
PERMISSIBLEMATERIALS
1. Non-programmable calculator.
 |
2 Page 2 |
▲back to top |
Question 1
Section A (13 marks]
Below are multiple choice questions and true/ false questions. Select the correct answer. [13]
1.1 A relative filename is a name that is selected by the File Manager when the file is created.
(True/False)
1.2 The key to the successful implementation of demand paging is the use of a high-speed CPU.
(True/False)
1.3 Context switching is required by all preemptive algorithms. (True/False)
1.4 A large job can have problems with a first-fit memory allocation scheme. (True/False)
1.5 A compressed image file can be reconstructed if a lossy compression algorithm is used
because the compression process is reversible. (True/False)
1.6 Although non-contiguous allocation schemes eliminate external storage fragmentation and
the need for compaction, they don't support direct access because there's no easy way to
determine the exact location of a specific record. (True/False)
1.7 In indexed storage, when a file is created, the pointers in the index block are all set to __ .
a) The end of the volume
b) The beginning of the volume
c) Null
d) zero
1.8 A file's __ filename includes all path information for that file.
a) Extended
b) Absolute
c) Relative
d) Long-form
Page 1 of6
 |
3 Page 3 |
▲back to top |
1.9 Which of the following is not an example of embedded system?
a) Point OF Sale (PoS)
b) Pacemakers
c)
Elevators
d) Automobiles
1.10 On an optical disc, all sectors are __ .
a) of varying sizes depending upon where you are on the disc.
b) larger as you move to the edge
c) smaller as you move to the edge
d) of the same size throughout the disc
1.11 __ is the policy of allowing only one process to have access to a dedicated resource.
a) No preemption
b) Mutual exclusion
c) Circular wait
d) Resource holding
1.12 The transition from __ is initiated by the Job Scheduler according to some predefined
policy. At this point, the availability of enough main memory and any requested devices is
checked.
a) READYto RUNNING
b) HOLDto READY
c) RUNNING to WAITING
d) RUNNING back to READY
1.13 __ peripheral devices are assigned to only one job at a time.
a) Dedicated
b) Shared
c) Virtual
d) Static
Page 2 of6
 |
4 Page 4 |
▲back to top |
Section B [28 marks]
Question 2
Define the following terms as used in operating systems:
2.1 Compaction
[2]
2.2 1/0 channel
[2]
Question 3
Describe the two benefits and two drawbacks of large and small partition sizes.
[4]
Question 4
4.1 Explain two benefits and two disadvantages of using a contiguous file allocation scheme. [4]
4.2 Name any three selection considerations that must be considered when choosing the type
of file organisation?
[3]
4.3 List any three items that can be found in a file descriptor table.
[3]
Question 5
5.1 Explain why Direct Memory Access (OMA) is considered an efficient mechanism for
performing 1/0 operations.
[2]
5.2 Explain how buffers are used in OMA?
[2]
Question 6
Given the criteria below, which process scheduling algorithm would best satisfy the following
requirements? Motivate your answer.
6.1 You want the most important jobs to always be processedfirst.
[2)
6.3 You want to minimize the average waiting time for all jobs.
[2)
6.4 You want to ensure fast completion of short jobs, while performing context switching. [2)
Page 3 of6
 |
5 Page 5 |
▲back to top |
Section C [39 marks]
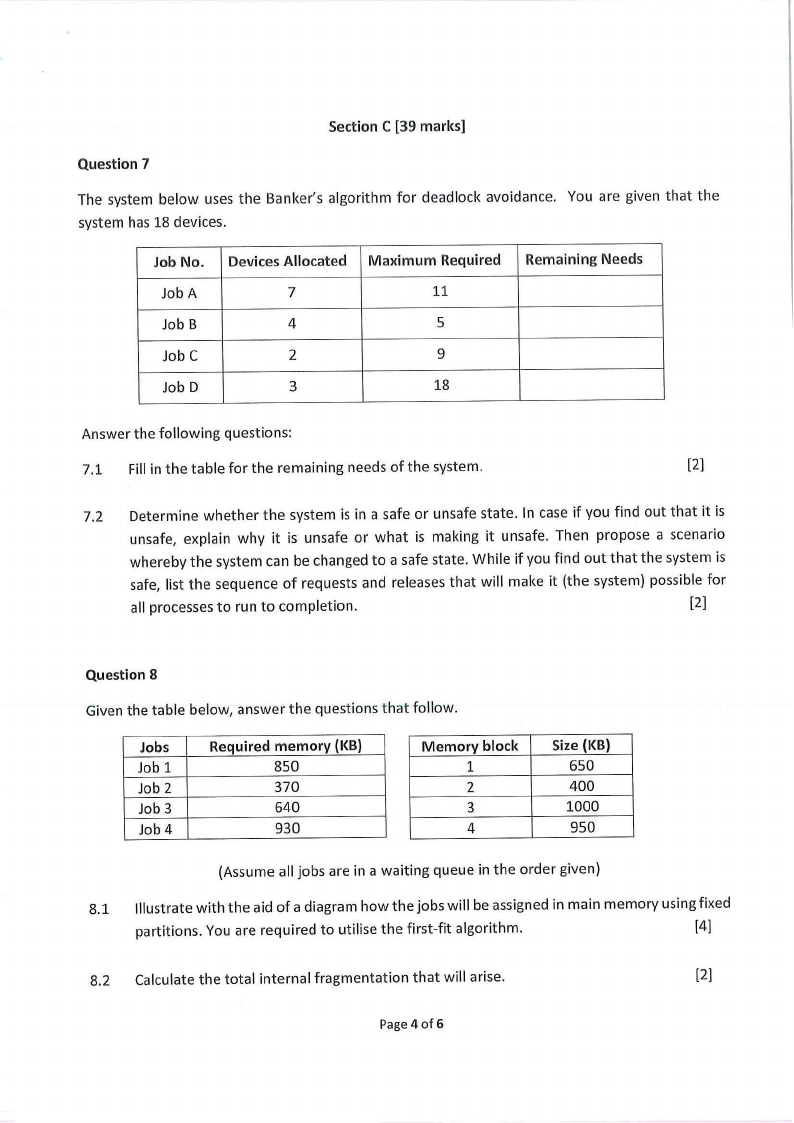
Question 7
The system below uses the Banker's algorithm for deadlock avoidance. You are given that the
system has 18 devices.
Job No.
Job A
Job B
Job C
Job D
Devices Allocated
7
4
2
3
Maximum Required
11
5
9
18
Remaining Needs
Answer the following questions:
7.1 Fill in the table for the remaining needs of the system.
[2]
7.2 Determine whether the system is in a safe or unsafe state. In case if you find out that it is
unsafe, explain why it is unsafe or what is making it unsafe. Then propose a scenario
whereby the system can be changed to a safe state. While if you find out that the system is
safe, list the sequence of requests and releases that will make it (the system) possible for
all processes to run to completion.
[2]
Question 8
Given the table below, answer the questions that follow.
Jobs
Job 1
Job 2
Job 3
Job 4
Required memory (KB)
850
370
640
930
Memory block
1
2
3
4
Size (KB)
650
400
1000
950
(Assume all jobs are in a waiting queue in the order given)
8.1 Illustrate with the aid of a diagram how the jobs will be assigned in main memory using fixed
partitions. You are required to utilise the first-fit algorithm.
[4]
8.2 Calculate the total internal fragmentation that will arise.
[2]
Page4 of 6
 |
6 Page 6 |
▲back to top |
Question 9
If a program has 1077 bytes and will be loaded into page frames of 200 bytes each, and the
instruction to be used is at byte 507, answer the following questions given that 1 MB = 1 line of
code:
9.1 How many pages are needed to store the entire job?
[2]
9.2 Compute the page number and exact displacement for each of the byte addresses where
the data is stored. (Remember that page numbering starts at zero).
[2]
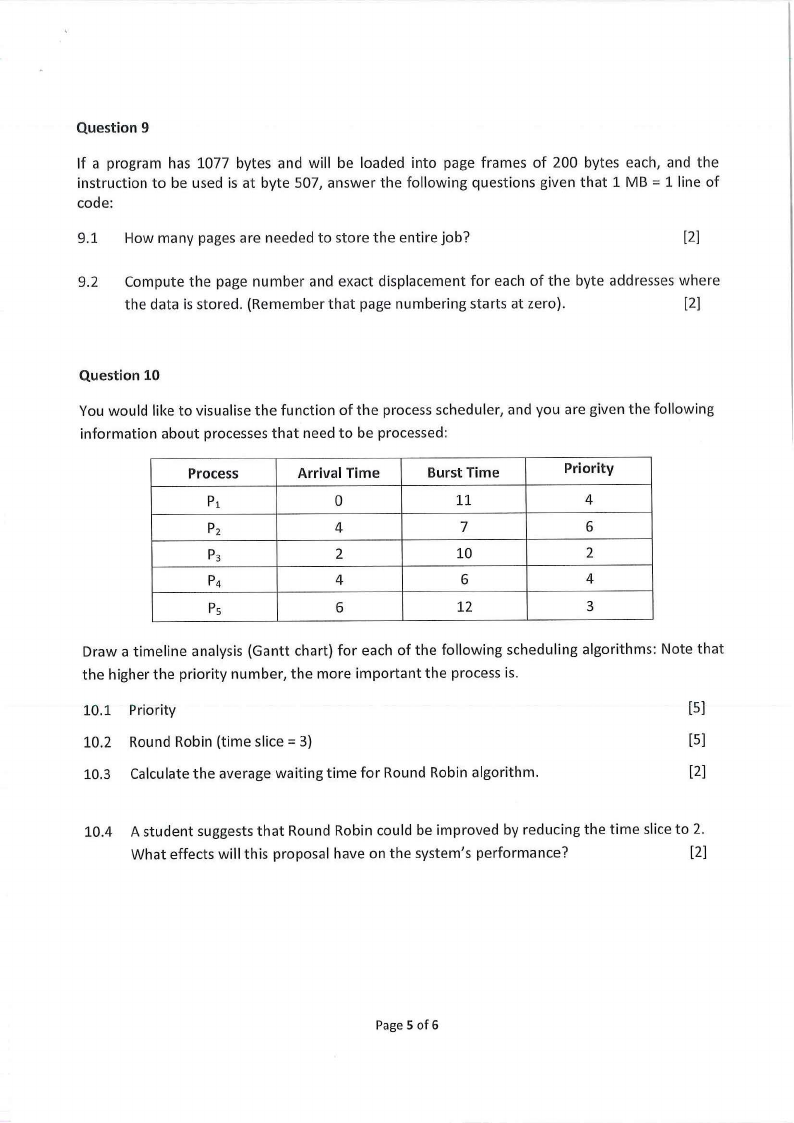
Question 10
You would like to visualise the function of the process scheduler, and you are given the following
information about processes that need to be processed:
Process
P1
P2
P3
P4
Ps
Arrival Time
0
4
2
4
6
Burst Time
11
7
10
6
12
Priority
4
6
2
4
3
Draw a timeline analysis (Gantt chart) for each of the following scheduling algorithms: Note that
the higher the priority number, the more important the process is.
10.1 Priority
[5]
10.2 Round Robin (time slice= 3)
[5]
10.3 Calculate the average waiting time for Round Robin algorithm.
[2]
10.4 A student suggests that Round Robin could be improved by reducing the time slice to 2.
What effects will this proposal have on the system's performance?
[2]
Page 5 of 6
 |
7 Page 7 |
▲back to top |
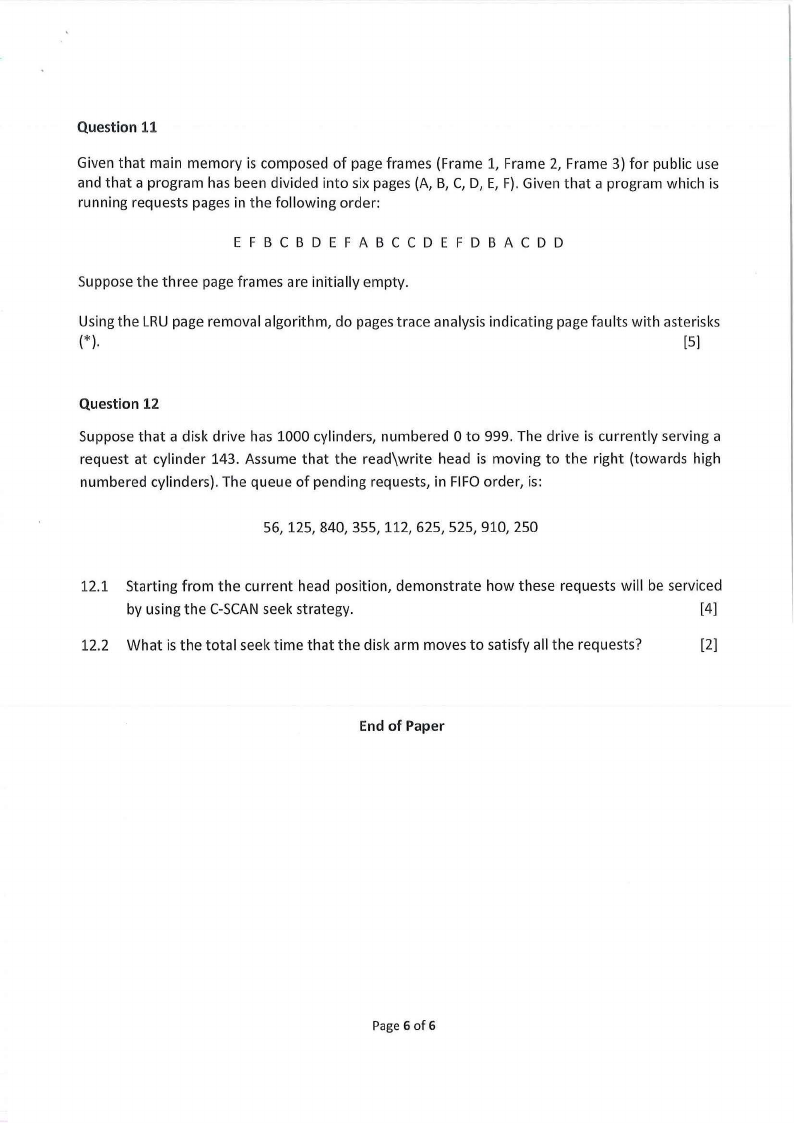
Question 11
Given that main memory is composed of page frames (Frame 1, Frame 2, Frame 3) for public use
and that a program has been divided into six pages (A, B, C, D, E, F). Given that a program which is
running requests pages in the following order:
EFBCBD EFA BCCD EFD BA CD D
Suppose the three page frames are initially empty.
Using the LRU page removal algorithm, do pages trace analysis indicating page faults with asterisks
(*).
[5]
Question 12
Suppose that a disk drive has 1000 cylinders, numbered Oto 999. The drive is currently serving a
request at cylinder 143. Assume that the read\\write head is moving to the right (towards high
numbered cylinders). The queue of pending requests, in FIFOorder, is:
56,125,840,355,112,625,525,910,250
12.1 Starting from the current head position, demonstrate how these requests will be serviced
by using the C-SCANseek strategy.
[4]
12.2 What is the total seek time that the disk arm moves to satisfy all the requests?
[2]
End of Paper
Page 6 of 6





